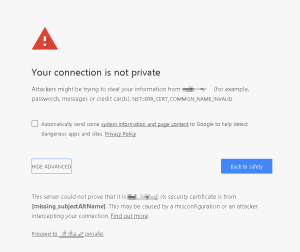
Recently I was upgrading a site to Sitecore 8.2.1, and I received the following error:

Okay, WTF? There’s not a lot of information about this error, and I’d never seen it before. I ended up doing my usual trick – decompiling Sitecore to see what this method does. Here’s what I found…

…and the bit underlined in red set my “stupidity radar” screaming. This line is:
string database = SiteContext.GetSite(Settings.Preview.DefaultSite).SiteInfo.Database;
If GetSite() returns null, you’ll get a null reference exception, because they didn’t bother to check the returned variable before trying to use its ‘SiteInfo’ property.
It does offer a clue, though. Our upgraded system lacks a site called ‘website‘. That is, in our config, under the <sites> node, there is no <site ... > called ‘website‘. However, the DefaultSite setting in Sitecore.config still had its default value of ‘website‘.

We changed it to the name of our site, and this error was resolved.