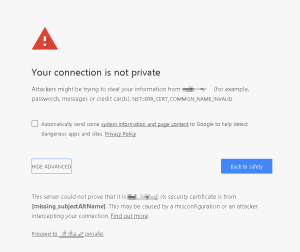
Finally, the web is really moving to using HTTPS (thank you Google/Chrome!) This change is long overdue, and it will be good to finally be able to eliminate the vulnerability of HTTP.
“But“, cry some customers, “I don’t wanna pay for certificates!“.
Bought TLS certificates, well, cost money, and often non-technical customers don’t see any value in them. All they see is cost. If only there were a free alternative.
Good news! LetsEncrypt freely offer free DV certificates for free. That is, in fact, their raison d’être. Bad news – they only last 90 days. Bugger. Our support team won’t dreadfully want to have to renew lots of certs every 90 days. If only this could be automated… Wait, it can be!
One of my colleagues mentioned using WinAcme to get/renew certificates with LetsEncrypt, so I thought I’d give it a go. How hard can it be? Continue reading “Using LetsEncrypt with IIS via WinAcme”