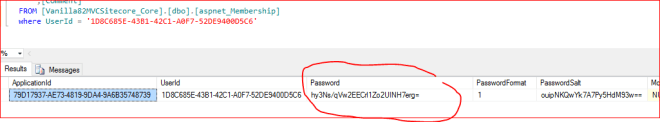
Previously I’ve posted how to do this – but it was a bit hacky. You had to know your Admin’s UserID, which can change between instances now. So, here’s the SQL to do it for any Sitecore\Admin user…
Update membership
set [Password] = '2hwfEqtM7gDFekQaV/IOkog5DFmxRtywvUsRJqRf7j82Ns3pUkiu/WohjLk8mIV2+7MjXdMeO9MgAUjildTLtg==',
[PasswordSalt] = 'ETJOU1+PX4CwEOw/eN3F6Q==',
[IsLockedOut] = 0,
[Comment] = 'Sitecore Administrator (512)'
from [aspnet_Membership] membership
INNER JOIN [aspnet_Users] users ON membership.UserId = users.UserId
WHERE users.UserName = 'sitecore\Admin'