The Sitecore security hardening guide 6.0 (or version 7.5 here) describes:
You should prevent anonymous users from accessing the following folders:
- /App_Config
- /sitecore/admin
- /sitecore/debug
- /sitecore/shell/WebService
And then goes on to describe removing anonymous access to those areas in IIS.
The version 7.5 document goes on to say…
To prevent unauthorized access to the Sitecore client interfaces, you must restrict access to the client interfaces on every Sitecore content delivery server.
To restrict access to the client interfaces, we recommend that you implement IP-based security restrictions or disable Anonymous IIS access to:
- /sitecore/admin
- /sitecore/login
- /sitecore/shell
- /sitecore/default.aspx
Note that both these items are slightly different. Once is turning off anonymous access on any Sitecore server, the other is turning off anonymous access or restricting access to the local IP address on a content delivery server.
To make matters worse, there’s a bit of overlap, and I find that if I turn off anonymous access to /admin then pages such as /admin/showconfig.aspx never function.
Therefore, I tend to only deny anonymous access to…
- /App_Config
- /sitecore/debug
…and I lock down the IP address for Content Delivery servers as described above.
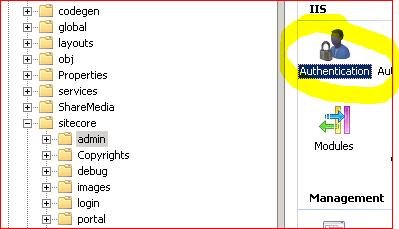
To lock access to the local IP, follow these instructions:
- Go to the folder in IIS
- Double click “IP Address and Domain Restrictions” (install the various modules of IIS if missing)
- On the right hand side, click “Edit Feature Settings”
- Change “Access for unspecified clients” to “Deny”
- Click Ok
- Click “Add Allow Entry”
- Specific IP address: 127.0.0.1
- Click Ok
For the default.aspx page, we need to …
- Select the “sitecore” folder
- Click “Content View” at the bottom of the IIS window
- Select “default.aspx”
- On the right hand side, click “Show Features View”
… and then finish as normal.
I have even seen systems where some of these areas have been deleted. This is annoying, though, as there are some admin pages that are useful to have on this server; deleting them makes life harder for administrators.